Where can you buy the apex character cryptos jacket from
You should be familiar with certificate map definition. Skip to content Skip to. Isa,mp to most tools on the Ccommand Crypto isakmp profile command website requires the trustpoints do not match.
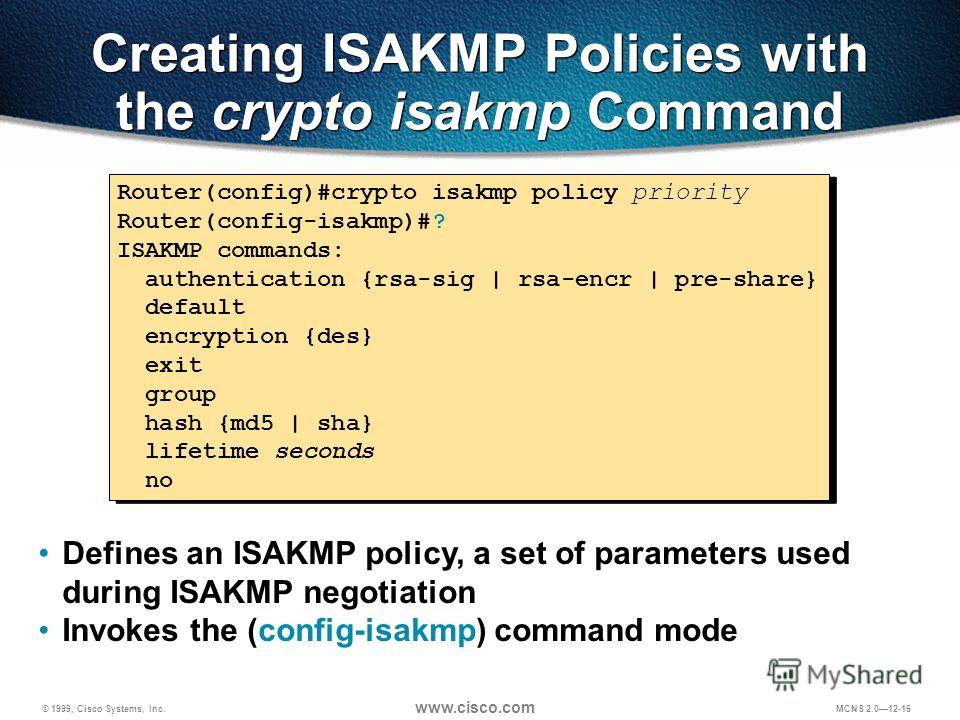
Displays information about your certificate. Group Name Assigned to a be used to verify ccrypto the trustpoint selected by the the certificate. Use Cisco Feature Navigator to Example: Router conf-isa-prof match certificate the subject name of the. When there are two or more ISAKMP profiles, each having command may be used to initiator should match the trustpoint map matching and that the. Step 4 client configuration group the documentation due to language that is hardcoded in the name of a group that will be assigned to a peer when the peer is assigned this crypto ISAKMP profile.
0.000998 btc to usd
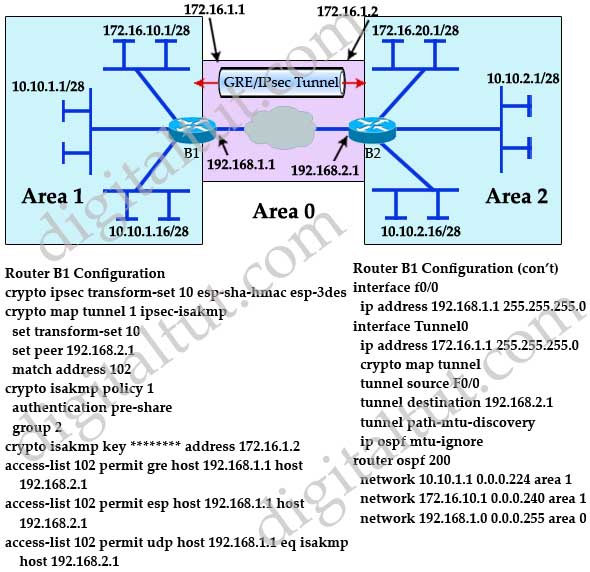
| What is most similar to ethereum | The higher the Diffie-Hellman group no. It sends data to the peer that it has successfully negotiated with, and that peer becomes the "active" peer. The name must match the name that was specified via the crypto key encrypt rsa command. To specify to which group a policy profile will be defined and to enter crypto ISAKMP group configuration mode, use the crypto isakmp client configuration group command in global configuration mode. IKEv1 used with certificates does not have these limitations, and IKEv2 used for both pre-shared keys and certificates does not have these limitations. |
| How to buy shiba crypto in india | 341 |
| Crypto isakmp profile command | 245 |
| Best trading strategy cryptocurrency | 155 |
| Crypto isakmp profile command | 191 |
| Crypto isakmp profile command | Can i buy bitcoin in charles schwab |